How EmDash Plugins Work: Sandboxed Capabilities Instead of Full Trust
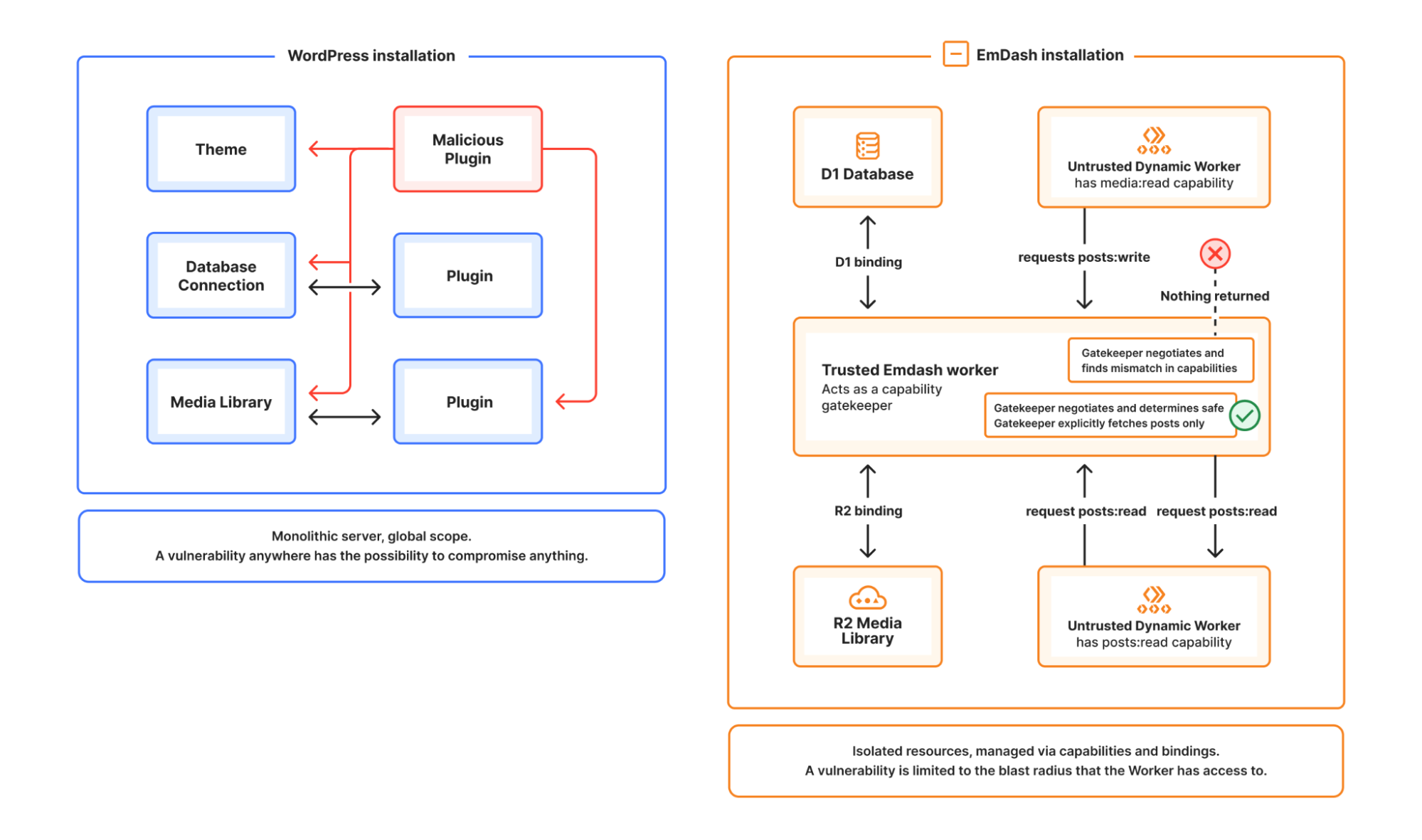
EmDash plugins are built around explicit capabilities and isolated execution, which gives administrators and plugin authors a much cleaner trust model than traditional CMS plugins.
The simplest way to understand EmDash plugins is this: they are not trusted by default with everything.
That sounds obvious, but it is the core design difference.
In many CMS ecosystems, a plugin becomes powerful because it shares the same broad runtime and inherits wide access to the application. EmDash moves in the opposite direction. A plugin starts narrow and expands only through declared capabilities.
What “sandboxed capabilities” means
An EmDash plugin is expected to tell the platform what it needs.
That usually includes two things:
- what hooks or lifecycle events it wants to respond to
- what capabilities it needs in order to do useful work
This is a better model for both operators and developers.
Operators get a clearer answer to “what does this plugin actually do?” Developers get a cleaner contract for how plugins should be written.
Why this is better than broad trust
A plugin that only needs to react to content publication should not silently inherit unrelated powers.
A constrained model produces better security outcomes because it narrows the space for accidental misuse. It also produces better review outcomes because you can evaluate scope before installation instead of inferring it from code behavior after the fact.
That changes plugin evaluation from vague trust to explicit permission review.
What this means for plugin authors
For authors, a capability-driven model is not just a security feature. It is a product design discipline.
It forces better questions early:
- What should this plugin be responsible for?
- What events should trigger it?
- What platform services does it truly need?
- What can stay outside the plugin entirely?
That usually leads to smaller and more focused extensions.
What this means for site administrators
For administrators, the biggest advantage is predictability.
A healthy plugin ecosystem is not built only on quantity. It is built on being able to install useful software without feeling like every new integration is a leap of faith.
EmDash’s approach supports that by making plugin scope easier to inspect, reason about, and govern.
That matters even more on teams where the person approving plugins is not the same person writing them.
A practical plugin review standard
If you are evaluating an EmDash plugin, these are the right questions to ask:
- Which lifecycle hooks does it subscribe to?
- Which capabilities does it request?
- Does that scope match the user-facing promise of the plugin?
- Does it need any network access, and if so, how tightly is that defined?
That is a much healthier review process than “it has a lot of installs, so it is probably fine.”
Why this matters for the ecosystem
Plugin ecosystems succeed when they encourage experimentation without demanding blind trust.
That is the longer-term value of sandboxed capabilities. They do not just reduce risk on one site. They make it more realistic for an ecosystem to grow without turning security review into permanent triage.
If you want the short version, it is this: EmDash plugins work because they are designed around declared scope, not inherited power.