Why WordPress Plugin Security Keeps Failing and What EmDash Changes
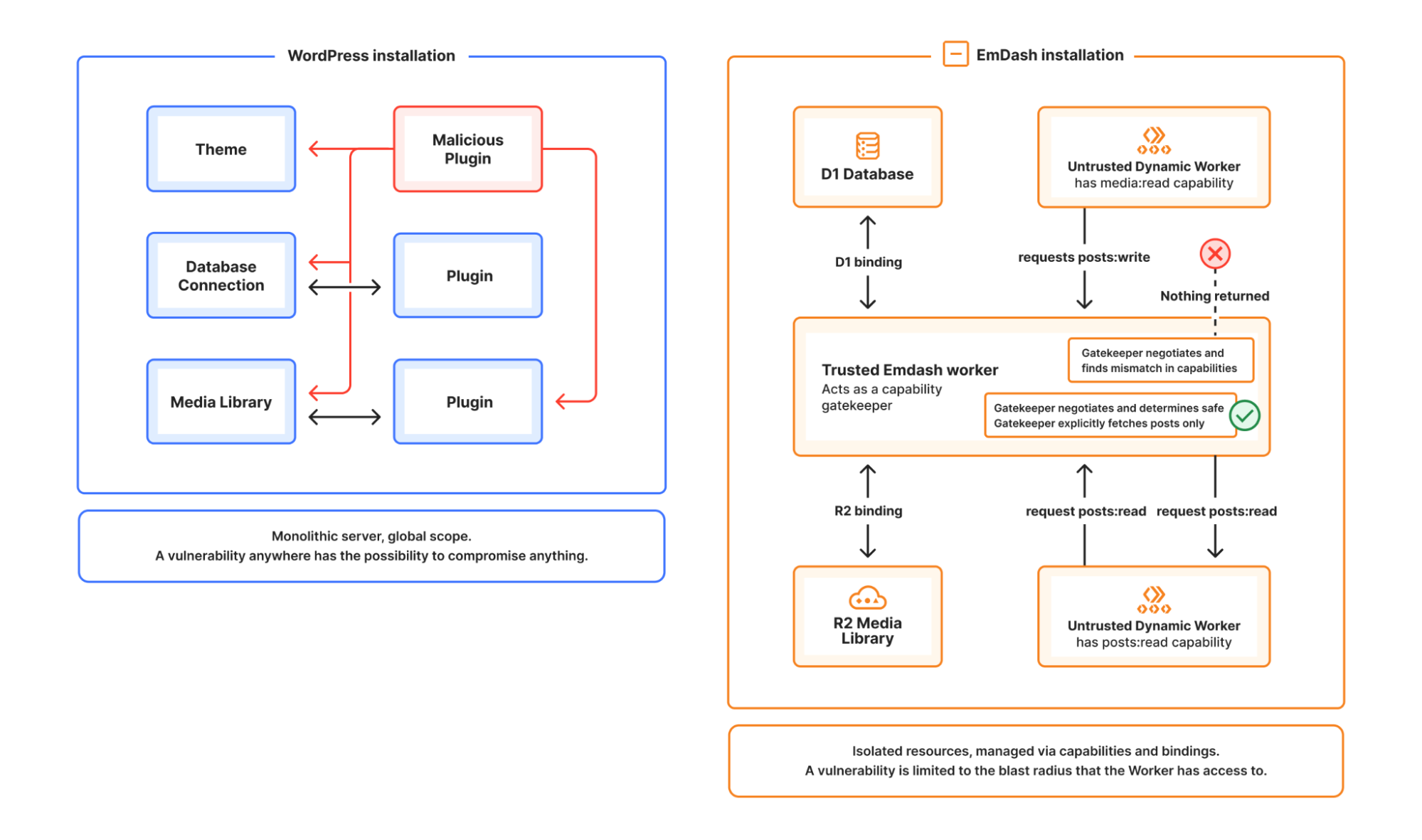
WordPress plugin risk is not just a quality problem. It is an execution model problem. EmDash changes the trust model by isolating plugins and granting only declared capabilities.
WordPress plugin security is often discussed as if the main problem were bad code, abandoned maintainers, or inconsistent review. Those issues are real, but they sit downstream of a more fundamental design choice: a WordPress plugin usually runs with far more authority than it should.
That means a plugin vulnerability is rarely confined to one small feature. It can become a site-wide problem because the plugin is operating in the same broad execution environment as the rest of the application.
Why the problem keeps repeating
The WordPress plugin ecosystem is huge because WordPress made extension easy. That openness created enormous value, but it also created a security model based on deep trust.
In practice, installing a plugin often means trusting it with:
- database access
- filesystem access
- broad execution hooks
- indirect exposure to arbitrary input from users, bots, and other plugins
At that point, security becomes a matter of hoping every plugin author makes consistently good decisions forever. That is not a scalable assumption for a large ecosystem.
The real issue is over-privilege
A plugin should not get broad authority just because it needs to perform one narrow task.
If a plugin sends an email after a post is published, the important question is not whether the plugin is popular. The important question is what that plugin can actually do.
A modern security model should let an administrator answer questions like:
- Can this plugin read content?
- Can it write content?
- Can it send email?
- Can it call external services?
- Can it touch anything outside the scope it declared?
WordPress was not designed around that kind of explicit permission boundary.
What EmDash changes
EmDash takes a different approach. Plugins run in isolated sandboxes and are expected to declare the capabilities they need up front.
That matters because it shifts plugin trust from vague reputation to visible scope.
A better plugin system is not one that promises perfect authors. It is one that limits the blast radius when authors make mistakes.
With an explicit capability model, you can reason about plugin risk more directly:
- a content automation plugin can be limited to content hooks and read access
- an email integration can be limited to sending mail
- network access can be narrowed to specific destinations instead of being assumed
This is a much better fit for teams that need a security review process rather than a plugin popularity contest.
Why this matters for real CMS operations
Most content teams do not have time to audit every plugin deeply. They still need integrations, publishing automations, previews, notifications, and editorial workflows. The practical question is whether the platform gives them a sane default trust model.
That is where EmDash has a stronger story. Instead of assuming that every plugin deserves broad access, it starts from the opposite position: access should be granted intentionally and narrowly.
That design choice does not remove the need for review, but it does make review more meaningful.
The bigger takeaway
The WordPress plugin security problem is not just about insecure plugins. It is about an ecosystem where plugins begin with too much trust.
EmDash does not solve that by asking for better behavior alone. It solves it by changing the execution model:
- isolate plugins
- declare capabilities
- grant only what is needed
- reduce the consequences of plugin mistakes
That is the difference between a plugin system that relies on hope and one that is built for constraint.